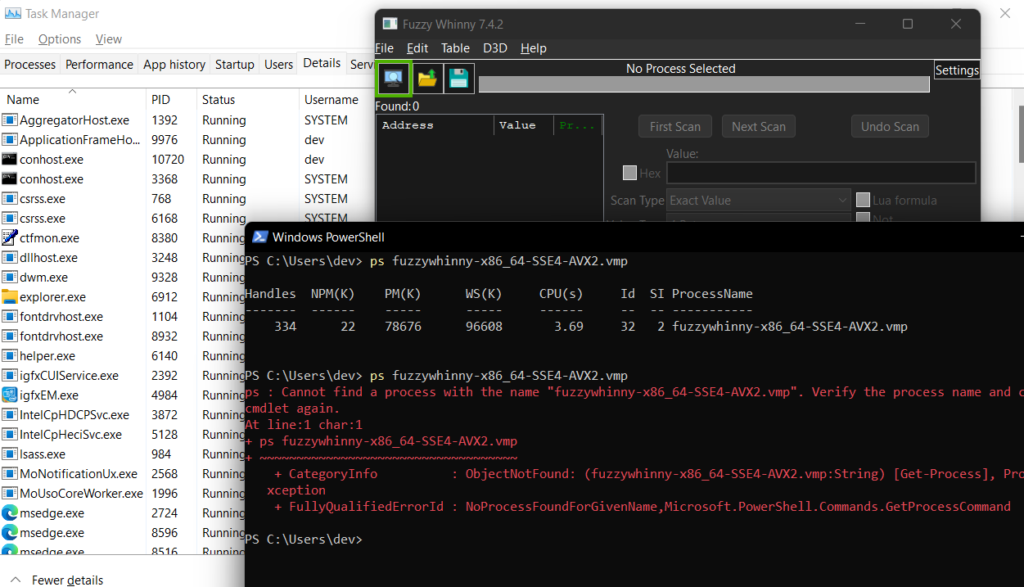
I am now close at finishing the HTB Junior Pentester role course but decided to take a quick brake and focus on one of my favorite fields: reversing games and evading anti-cheat.
The goal
The end goal is simple, to bypass the Cheat Engine for usermode anti-cheats and allow us to debug a game using type-1 hypervisor.
This writeup will be divided into 3 parts.
- First will be the concept of Direct Kernel Object Manipulation to make a process unlink from eprocess struct.
- Second, the concept of hypervisor for debugging.
- And lastly, is the concept of Patchguard, Driver Signature Enforcement and how to disable those.
So without further ado, let’s get our hands dirty!
Difference Between Kernel mode and User mode
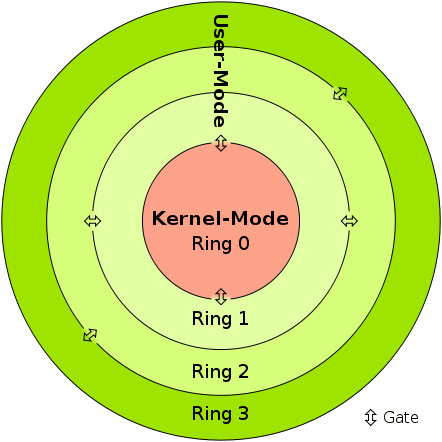
| Kernel-mode vs User mode | In kernel mode, the program has direct and unrestricted access to system resources. | In user mode, the application program executes and starts. |
|---|---|---|
| Interruptions | In Kernel mode, the whole operating system might go down if an interrupt occurs | In user mode, a single process fails if an interrupt occurs. |
| Modes | Kernel mode is also known as the master mode, privileged mode, or system mode. | User mode is also known as the unprivileged mode, restricted mode, or slave mode. |
| Virtual address space | In kernel mode, all processes share a single virtual address space. | In user mode, all processes get separate virtual address space. |
| Level of privilege | In kernel mode, the applications have more privileges as compared to user mode. | While in user mode the applications have fewer privileges. |
| Restrictions | As kernel mode can access both the user programs as well as the kernel programs there are no restrictions. | While user mode needs to access kernel programs as it cannot directly access them. |
| Mode bit value | The mode bit of kernel-mode is 0. | While; the mode bit of user-mode is 3. |
| Memory References | It is capable of referencing both memory areas. | It can only make references to memory allocated for user mode. |
| System Crash | A system crash in kernel mode is severe and makes things more complicated. | In user mode, a system crash can be recovered by simply resuming the session. |
| Access | Only essential functionality is permitted to operate in this mode. | User programs can access and execute in this mode for a given system. |
| Functionality | The kernel mode can refer to any memory block in the system and can also direct the CPU for the execution of an instruction, making it a very potent and significant mode. | The user mode is a standard and typical viewing mode, which implies that information cannot be executed on its own or reference any memory block; it needs an Application Protocol Interface (API) to achieve these things. |
Basically, if the anti-cheat resides only in usermode, then the anti-cheat doesn’t have the total control of the system. If you manage to get into the kernelmode, then you can easily manipulate all objects and events in the usermode. However, it is not advised to do the whole cheat in the kernel alone. One single mistake can cause Blue Screen Of Death, but we do need the kernel to allow us for easy read and write on processes.
EPROCESS
The EPROCESS structure is an opaque structure that serves as the process object for a process.
Some routines, such as PsGetProcessCreateTimeQuadPart, use EPROCESS to identify the process to operate on. Drivers can use the PsGetCurrentProcess routine to obtain a pointer to the process object for the current process and can use the ObReferenceObjectByHandle routine to obtain a pointer to the process object that is associated with the specified handle. The PsInitialSystemProcess global variable points to the process object for the system process.
Note that a process object is an Object Manager object. Drivers should use Object Manager routines such as ObReferenceObject and ObDereferenceObject to maintain the object’s reference count.
https://learn.microsoft.com/en-us/windows-hardware/drivers/kernel/eprocess
Interestingly, the EPROCESS contains an important handle that can enumerate the running process.
This is where the magic comes in.
typedef struct _EPROCESS
{
KPROCESS Pcb;
EX_PUSH_LOCK ProcessLock;
LARGE_INTEGER CreateTime;
LARGE_INTEGER ExitTime;
EX_RUNDOWN_REF RundownProtect;
PVOID UniqueProcessId;
LIST_ENTRY ActiveProcessLinks;
ULONG QuotaUsage[3];
ULONG QuotaPeak[3];
ULONG CommitCharge;
ULONG PeakVirtualSize;
ULONG VirtualSize;
LIST_ENTRY SessionProcessLinks;
PVOID DebugPort;
union
{
PVOID ExceptionPortData;
ULONG ExceptionPortValue;
ULONG ExceptionPortState: 3;
};
PHANDLE_TABLE ObjectTable;
EX_FAST_REF Token;
ULONG WorkingSetPage;
EX_PUSH_LOCK AddressCreationLock;
...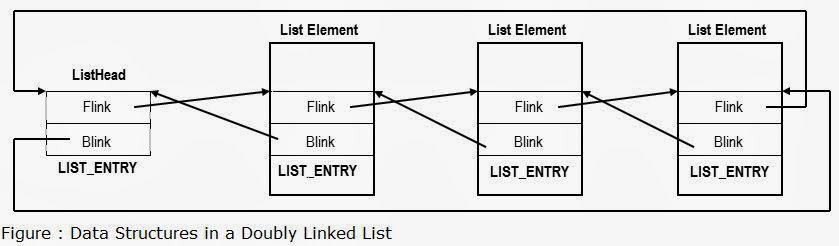
Each list element in LIST_ENTRY is linked towards the next application pointer (flink) and also backwards (blink) which then from a circular list pattern. Each application opened is added to the list, and removed also when closed.
Now here comes the juicy part!
Unlinking the process
Basically, removing the pointer of an application in the ActiveProcessLinks, means the application will now be invisible from other process enumeration. But don’t get me wrong. This is still detectable especially when an anti-cheat have kernel driver because they can easily scan for unlinked patterns and/or perform memory pattern scanning.
A lot of rootkits use this method to hide their process.
Visualization
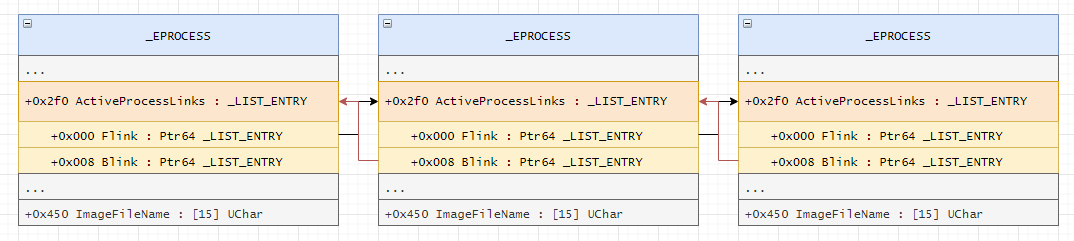
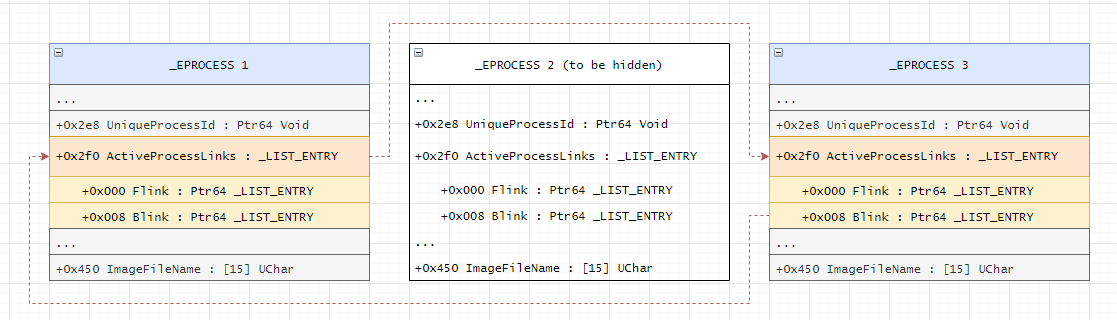
Checkout this link for image credits and for also a different perspective of the attack.
Kernel Driver
NTSTATUS processHiderDeviceControl(PDEVICE_OBJECT, PIRP irp) {
auto stack = IoGetCurrentIrpStackLocation(irp);
auto status = STATUS_SUCCESS;
switch (stack->Parameters.DeviceIoControl.IoControlCode) {
case IOCTL_PROCESS_HIDE_BY_PID:
{
const auto size = stack->Parameters.DeviceIoControl.InputBufferLength;
if (size != sizeof(HANDLE)) {
status = STATUS_INVALID_BUFFER_SIZE;
}
const auto pid = *reinterpret_cast<HANDLE*>(stack->Parameters.DeviceIoControl.Type3InputBuffer);
PEPROCESS eprocessAddress = nullptr;
status = PsLookupProcessByProcessId(pid, &eprocessAddress);
if (!NT_SUCCESS(status)) {
KdPrint(("Failed to look for process by id (0x%08X)\n", status));
break;
}Here, we can see that we are finding the eprocessAddress by using PsLookupProcessByProcessId.
We will also get the offset by finding the pid in the struct. We know that ActiveProcessLinks is just below the UniqueProcessId. This might not be the best possible way because it may break on the future patches when a new element is inserted below UniqueProcessId.
Here is a table of offsets used by different windows versions if you want to use manual offsets rather than the method above.
| Win7Sp0 | 0x188 |
| Win7Sp1 | 0x188 |
| Win8p1 | 0x2e8 |
| Win10v1607 | 0x2f0 |
| Win10v1703 | 0x2e8 |
| Win10v1709 | 0x2e8 |
| Win10v1803 | 0x2e8 |
| Win10v1809 | 0x2e8 |
| Win10v1903 | 0x2f0 |
| Win10v1909 | 0x2f0 |
| Win10v2004 | 0x448 |
| Win10v20H1 | 0x448 |
| Win10v2009 | 0x448 |
| Win10v20H2 | 0x448 |
| Win10v21H1 | 0x448 |
| Win10v21H2 | 0x448 |
auto addr = reinterpret_cast<HANDLE*>(eprocessAddress);
LIST_ENTRY* activeProcessList = 0;
for (SIZE_T offset = 0; offset < consts::MAX_EPROCESS_SIZE / sizeof(SIZE_T*); offset++) {
if (addr[offset] == pid) {
activeProcessList = reinterpret_cast<LIST_ENTRY*>(addr + offset + 1);
break;
}
}
if (!activeProcessList) {
ObDereferenceObject(eprocessAddress);
status = STATUS_UNSUCCESSFUL;
break;
}
KdPrint(("Found address for ActiveProcessList! (0x%08X)\n", activeProcessList));
if (activeProcessList->Flink == activeProcessList && activeProcessList->Blink == activeProcessList) {
ObDereferenceObject(eprocessAddress);
status = STATUS_ALREADY_COMPLETE;
break;
}
LIST_ENTRY* prevProcess = activeProcessList->Blink;
LIST_ENTRY* nextProcess = activeProcessList->Flink;
prevProcess->Flink = nextProcess;
nextProcess->Blink = prevProcess;We also want the process-to-be-hidden to link on its own because the pointer might not exists anymore if the linked process dies.
activeProcessList->Blink = activeProcessList;
activeProcessList->Flink = activeProcessList;
ObDereferenceObject(eprocessAddress);
}
break;
default:
status = STATUS_INVALID_DEVICE_REQUEST;
break;
}
irp->IoStatus.Status = status;
irp->IoStatus.Information = 0;
IoCompleteRequest(irp, IO_NO_INCREMENT);
return status;
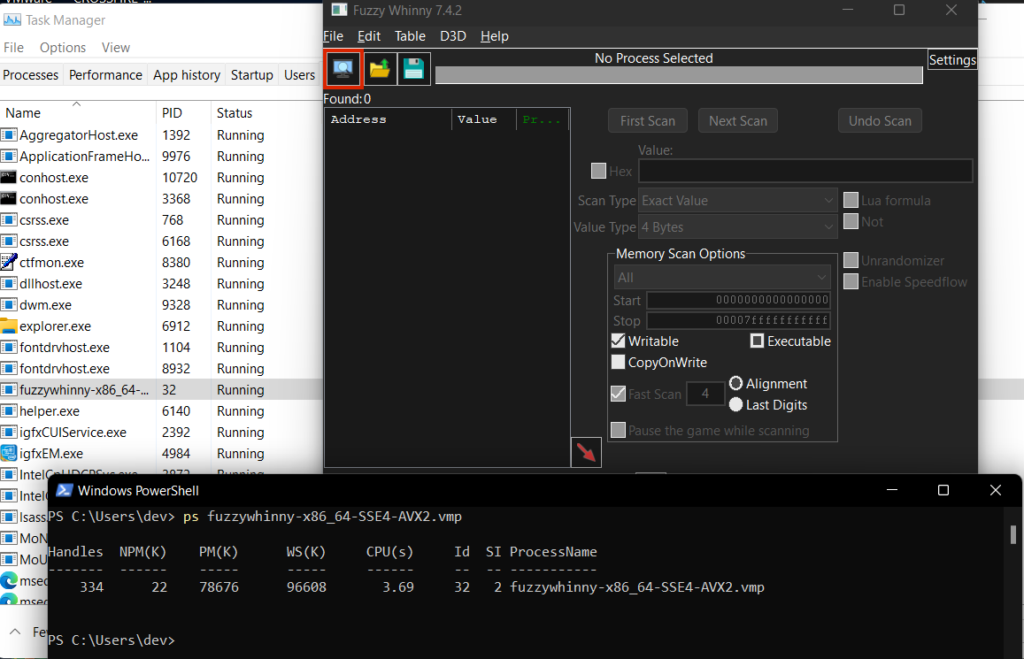
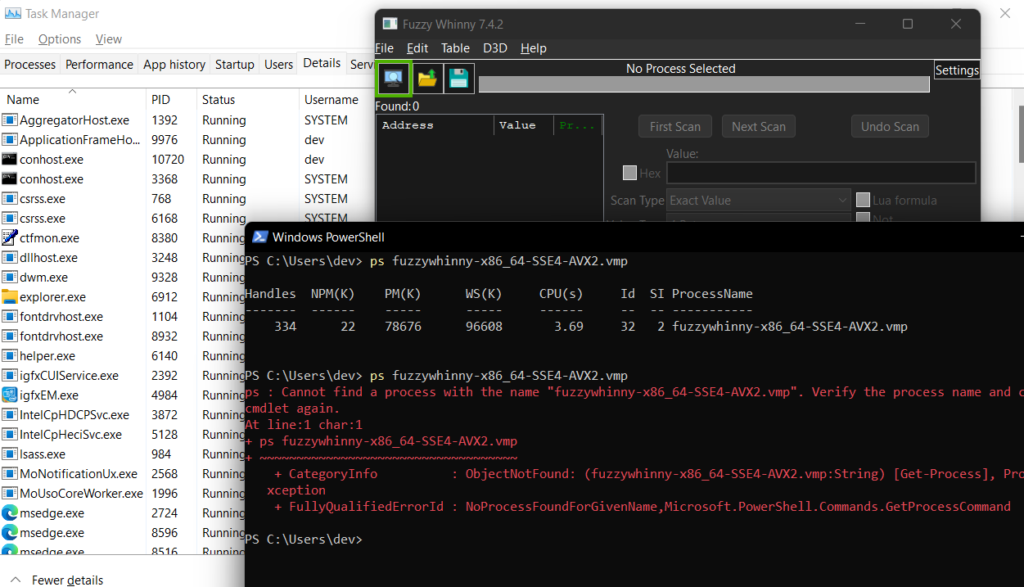
}POC
Warnings
There are 2 problems that you need to solve first before being able to do this method.
First: You need to disable Driver Signature Enforcement
You need to load your driver to be able to execute kernel functions. You either buy a certificate to sign your own driver so you do not need to disable DSE or you can just disable DSE from windows itself. The only problem of disabling DSE is that some games requires you to have enabled DSE before playing.
Second: Bypass Patchguard
Manually messing with DKOM will result you to BSOD. They got a tons of checks. But luckily we have some ways to bypass patchguard.
These 2 will be tackled on the 3rd part of the writeup. Stay tuned!